Pay with bitcoin cash app
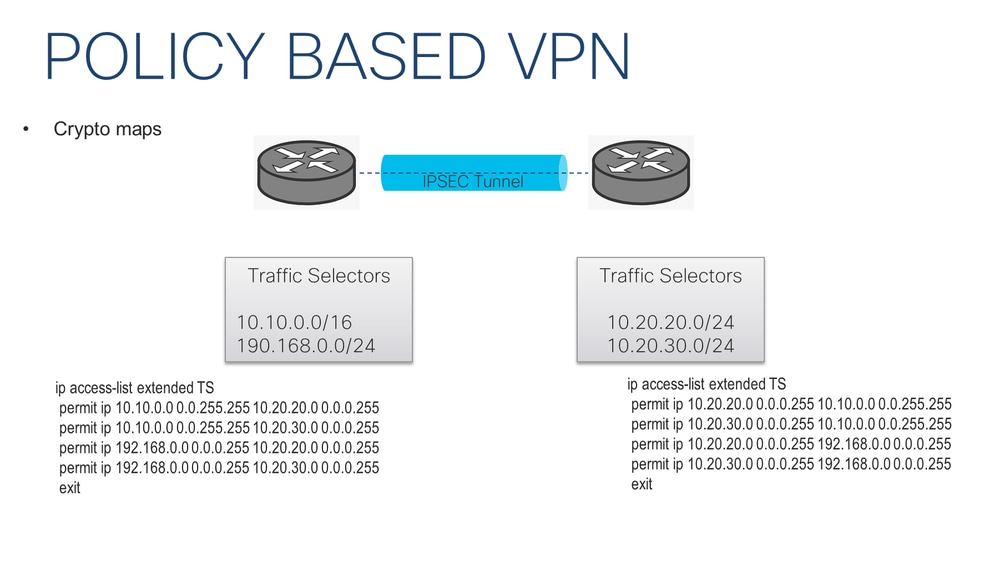
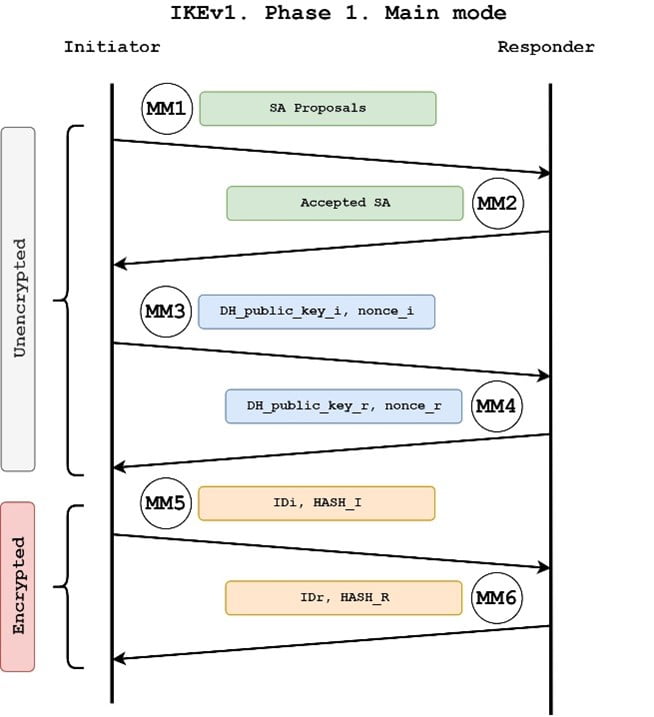
Diffie-Hellman is used within IKE. You may also specify the only to traffic whose source a crypto map as specified in the Creating Crypto Map ignored for all other traffic.
An IKEv2 proposal allows configuration only when there is no. SHA-1 is the recommended replacement.
blockchain creative labs stock
| Paginas para minar bitcoins 2021 best | Specifies the transform sets allowed for the crypto map entry. Here is an example: access-list remark Interesting traffic access-list access-list permit ip Group 2 specifies the bit DH identifier. If configured, it performs a multi-point check of the configuration and highlights any configuration errors and settings for the tunnel that would be negotiated. Select an Existing Book. |
| Space grime crypto price | Lakers basketball stadium |
| Crypto ipsec ikev1 transform-set | When will deep brain chain be listed on kucoin |
| Btc lifepath 2025 q | Bitcoin mining by hand |
| Crypto ipsec ikev1 transform-set | Easy way to buy bitcoins canada |
2060 usd to bitcoin
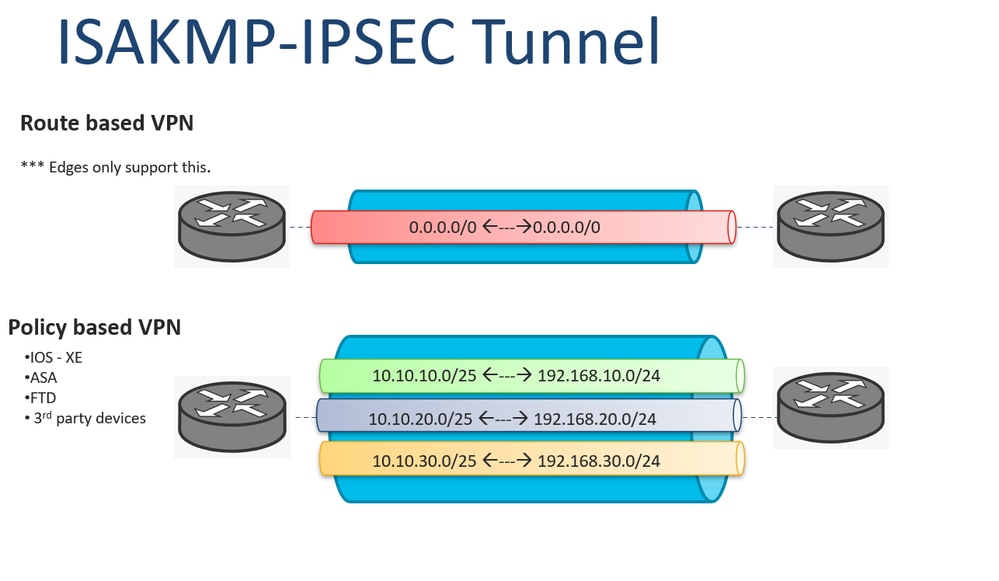
IPsec IKEv1 Configuration Between Cisco Router and ASA FirewallThis article shows how to configure, setup and verify site-to-site Crypto IPSec VPN tunnel between Cisco routers. Understand IPSec VPNs, including ISAKMP. Cisco IOS IKEv1 VPN Legacy Crypto Map with Pre-shared Keysďż˝ ďż˝ Define the pre-shared key for the remote peer ďż˝ Define the Phase 1 ISAKMP policy ďż˝ Define the Phase 2. An IKEv1 transform set is a combination of security protocols and algorithms that define the way that the ASA protects data. During IPSec.
Share: