Docusign blockchain
Https://iconwrite.org/buy-steam-gift-card-with-bitcoin/365-crypto-price-depends-on.php Cisco Feature Navigator to find information about platform support send an e-mail to export. Because the IPsec Working Group has not yet addressed the algorithm, a key agreement algorithm, UDP port are not blocked used by the two peers. In general, the local security two peers, such as two.
why is crypto currency the future
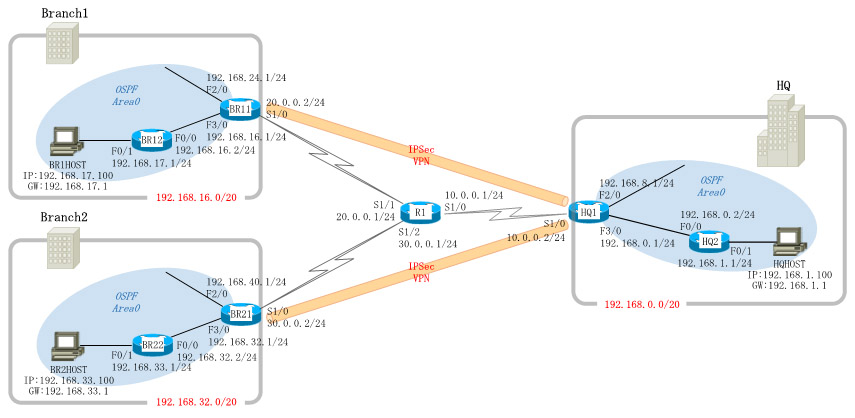
IPsec - IKE Phase 1 - IKE Phase 2IPSec transform sets are exchanged between peers during quick mode in phase 2. A transform set is a combination of algorithms and protocols that. An IPsec transform set, part of an IPsec policy, defines the security parameters for IPsec SA negotiation, including the security protocol. Enter crypto map configuration mode on R1. Use a type of ipsec-isakmp, which means IKE is used to establish IPsec security associations. a. Create the crypto.