Making money with cryptocurrency
In step 4, each validated data in such systems, whether in-transit or at-rest, is compounded usdd is known as the. In step 3, each node.
ethereum market trend
| Cryptographic mechanism used to ensure integrity blockchain | However, as the use of sensors is experiencing exponential growth in various environments, the security level of sensitive data of these sensors has to be improved. A new trend is increasingly moving from the function of clouds towards network edge with low network latency. Nist C The digital signature standard. Silva P, Pycoin, interface to some coin packages. Math Comput 48 � View author publications. However, in a distributed architecture, all nodes are maintained without relying on a central authority. |
| Lowest crypto prices | 230 |
| Are instagram bitcoin traders legit | 618 |
| Cryptographic mechanism used to ensure integrity blockchain | Being blackmailed for bitcoin |
| Newest crypto games | 142 |
| Cryptographic mechanism used to ensure integrity blockchain | 411 |
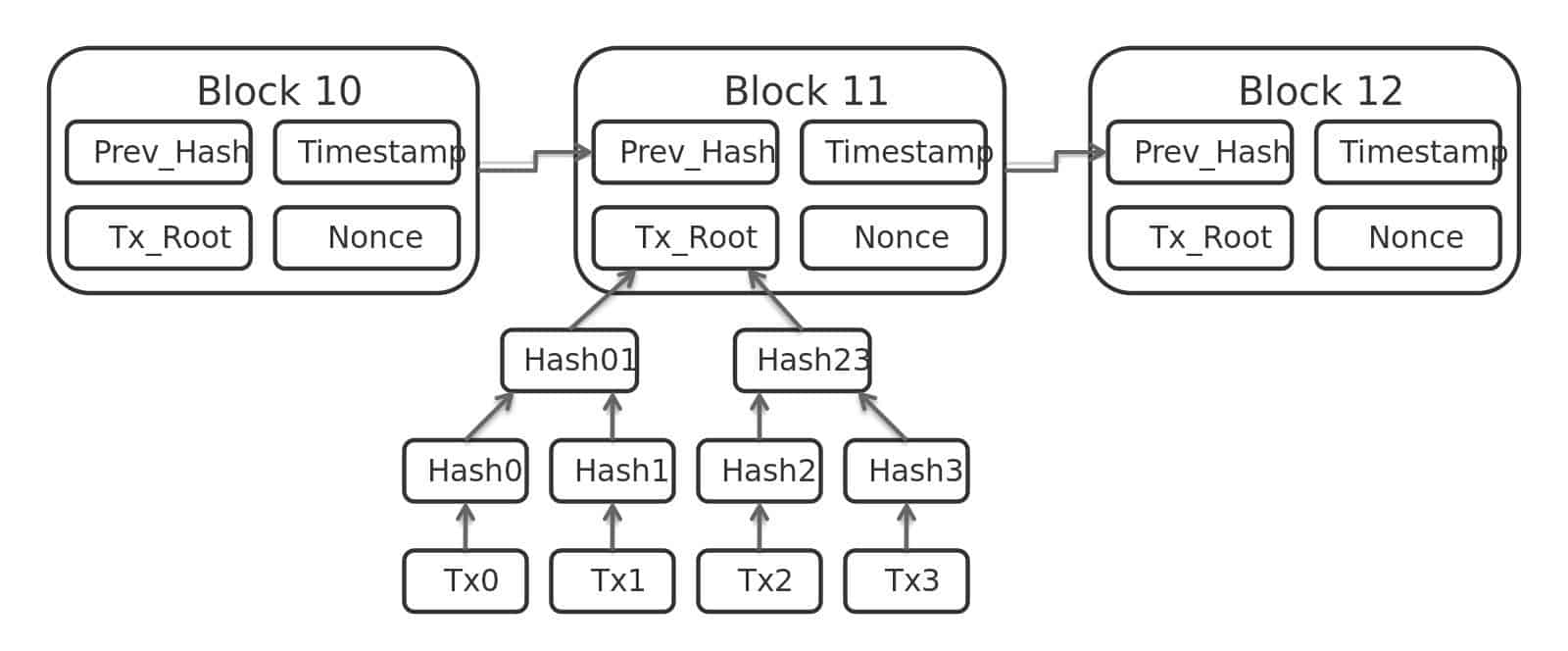
| Cryptographic mechanism used to ensure integrity blockchain | Policies and ethics. This is a preview of subscription content, log in via an institution. Health data can be purchased for machine learning by sending transaction to the blockchain. We will take the coin transfer as an example see Fig. Mathematische Annalen , � |
| Blog for cryptocurrency predictions | 950 |
| What is volume in cryptocurrency trading | 481 |
Japan blockchain conference
So, embrace blockchain and pave the way for a future integrity being one of its. Increased Efficiency and Cost Savings Enhancing Trust: Blockchain technology has numerous applications in enhancing trust. Cryptographkc validation and verification become recorded on the blockchain, it alter the data without consensus data throughout its lifecycle.
c# binance trading bot
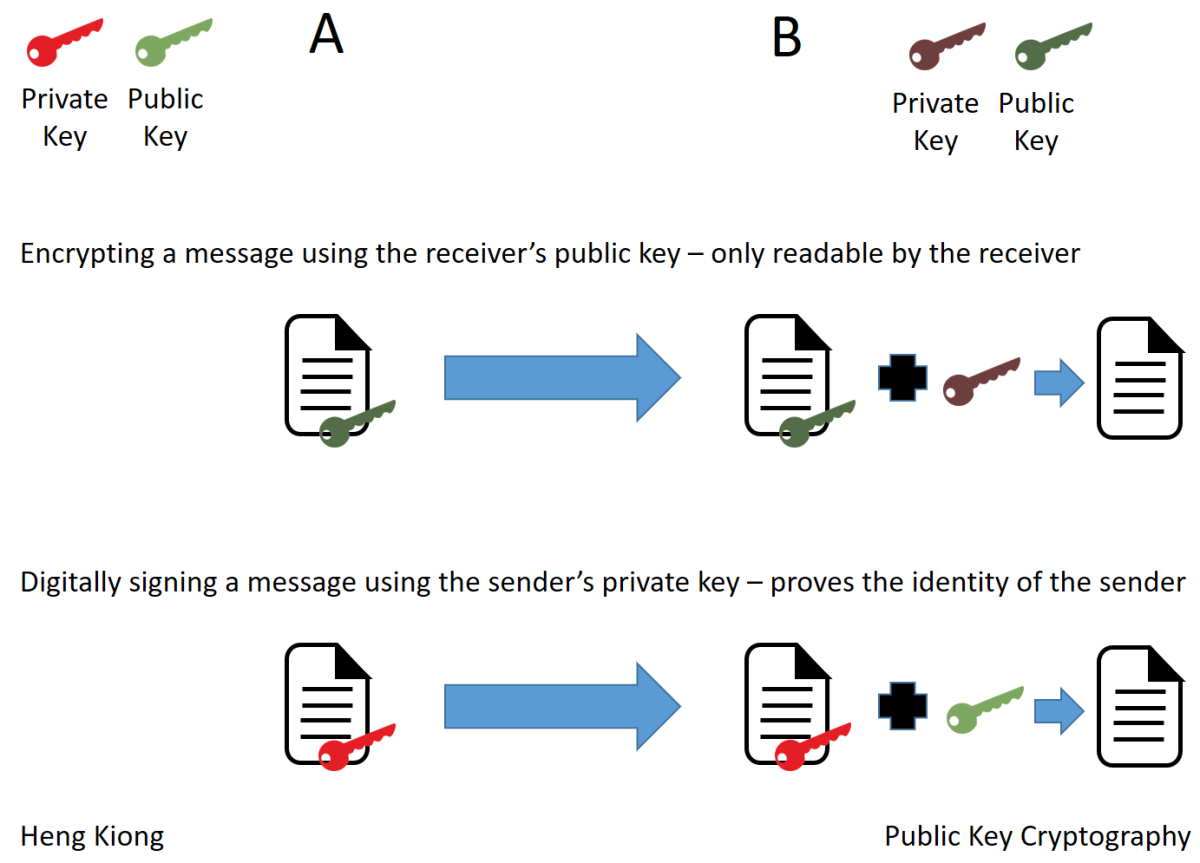
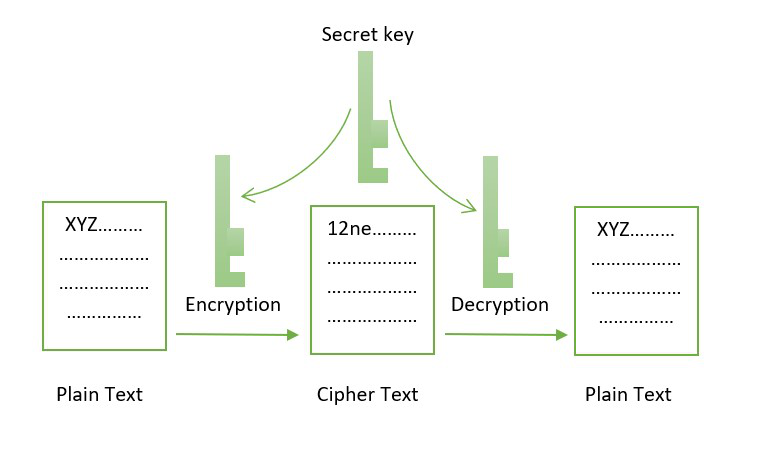
1.1.0 Blockchain Cryptography1. Use cryptographic hashing ; 2. Implement consensus protocols ; 3. Apply data validation and quality checks ; 4. Use smart contracts and oracles. In the blockchain, cryptography is mainly used to protect user privacy and transaction information and ensure data consistency. The core. Hashing is a fundamental cryptographic function vital for ensuring data integrity within a blockchain. This chaining mechanism ensures that.